

Clément Hallet - Full Stack Developer
As we access more and more software and applications that require the use of credentials, the multiplication of identification procedures and interfaces has become a real source of inefficiency for users. In this context of saturation, the emergence of Single Sign-On (SSO) is a solution to this problem and InUse now offers this possibility to its users.
A SSO (Single Sign-On) allows to share the identification of users between several applications. This means that the main application is the only one to hold the authentication data of its users, which it shares with authorized third-party applications when they request it. Users then only have to create an account once and only have to remember one password. The effort of complexity on this single password is thus promoted, indirectly making authentication more secure. Similarly, a compromised account only needs to be deactivated once to restrict all related access.
InUse now offers such an authentication system, based on the SAML (Security Assertion Markup Language) protocol. This is a standard for which many implementations softwares or application modules exist. The InUse application is then assimilated to the Identity Provider (IDP) to which additional services (SP) will be integrated.
While various types of incidents can cause machines to break down, it is sometimes necessary to call on the expertise of maintenance teams to make a diagnosis. If no solution is found internally, it is necessary to call on the equipment manufacturer or a maintainer to intervene, either remotely or on site. This intervention imposes an additional delay for the repair, even more so if it takes place in a foreign factory. So how can we improve the autonomy of operators so that they can diagnose or resolve an unexpected incident without resorting to third-party assistance?
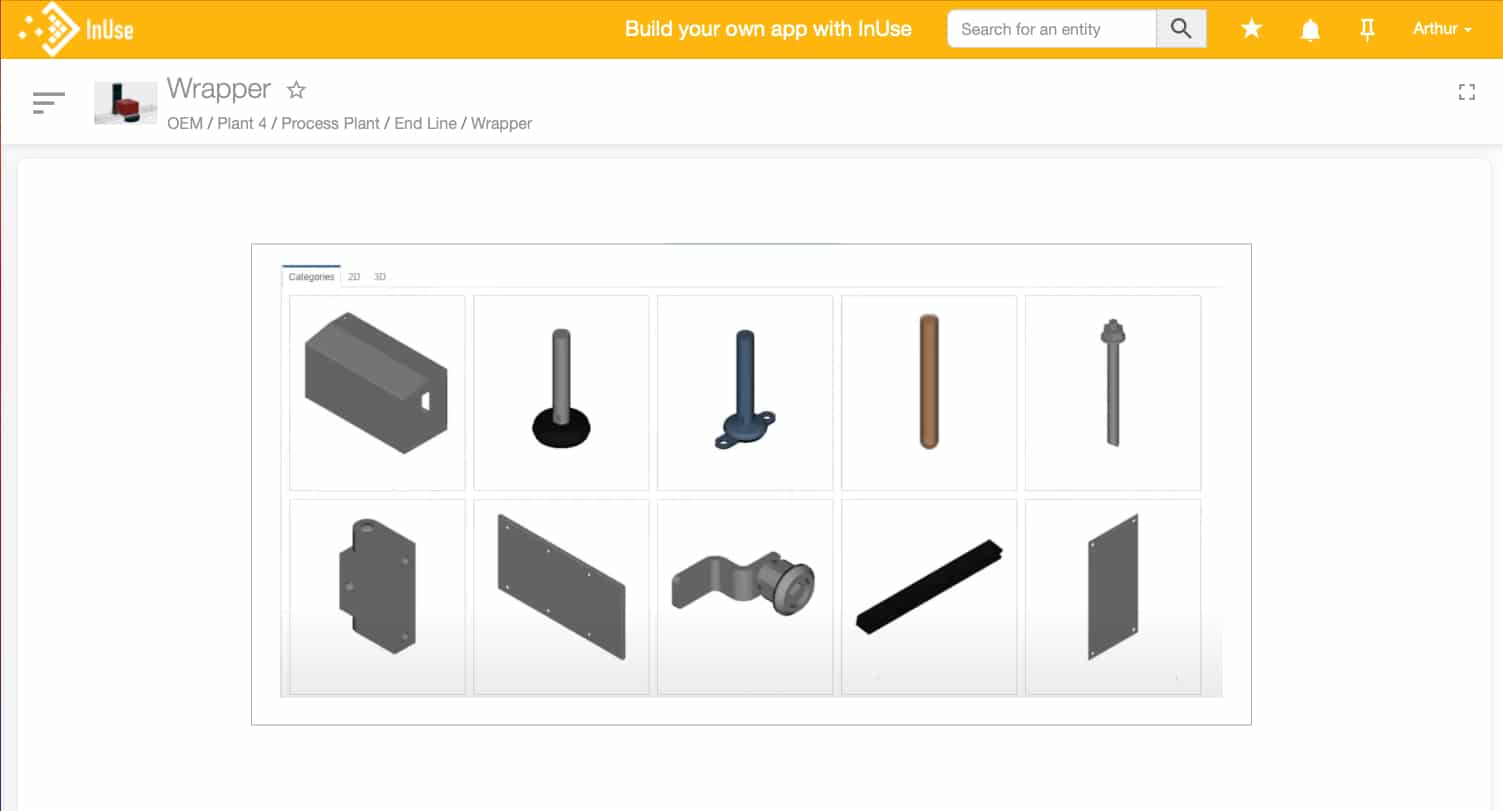
Example of third party application integration within the InUse solution: here a spare parts catalog
Even if the InUse solution helps manufacturers to better operate equipment thanks to useful and actionable insights in the field, the outcome of these actions may however require the use of other applications of your information system.
With this in mind, InUse now offers to integrate access to some of your related applications directly from the solution. The SSO will ensure a common repository for user identification. This repository can be supplemented by a shared nomenclature for machine identification, for example. The third-party application will then be able to adapt its content according to the user and the context from which he has performed his action. Here are some concrete examples:
Beyond these examples, others will be offered directly by InUse through specific partnerships. In addition, each company using the solution will be able to directly integrate access to some of its applications.
Implementing an SSO is quick and easy, as long as you follow these steps with the help of your IT department:
Implementing the SAML authentication protocol in the target application (e.g. a spare parts catalog, a CMMS,…) or from a service provider is the first step to interface with the InUse application. The target application will then be able to emit a metadata file that allows InUse to recognize it as a Service Provider (SP) and to specify the technical ways and means for sharing user authentication: communication protocol, user data allowing identification.
This operation is bidirectional and the metadata file provided by InUse on behalf of its clients will allow the third party application to register it as Identity Provider (IdP). These metadata files usually take the form of a url to be queried by the other party, thus allowing regular updates.
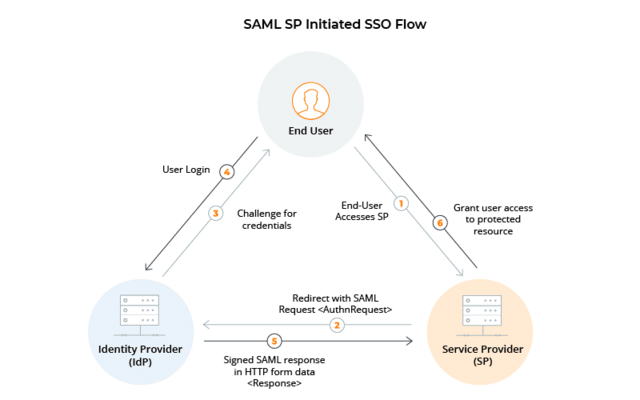
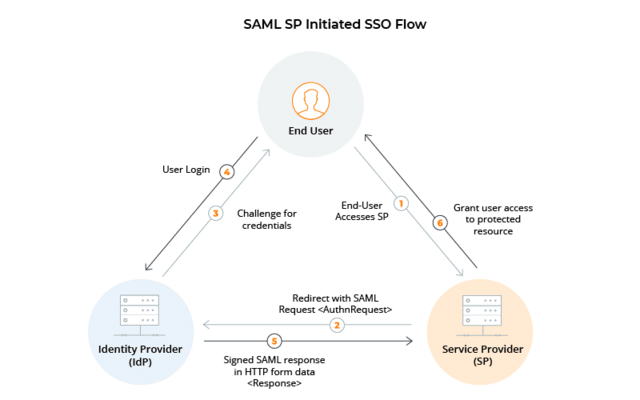
Scheme of operation of a SAML authentication : the metadatas exchanged beforehand allow the servers (IdP and SP) to establish this process.
Once this interconnection has been made, the target application will be directly integrated into the InUse application (iframe). The choice of the context in which it will be accessible can be configured directly from the Studio’s Publish module. It will allow you to define in particular:
ou are an InUse user and wish to set up this authentication system? We invite you to contact your Customer Success representative 🙂
You are an editor and would like to study the possibility of integrating your application into our solution?
Additional bibliography :
Related News
